Cloud infrastructure powers much of today’s digital world. Businesses store customer data, financial records, and internal systems in cloud environments and data centers. These systems help companies scale quickly and manage large amounts of information.
However, every piece of infrastructure has a lifecycle. Servers are replaced. Storage devices are retired. Entire cloud environments may be decommissioned when companies migrate to new platforms.
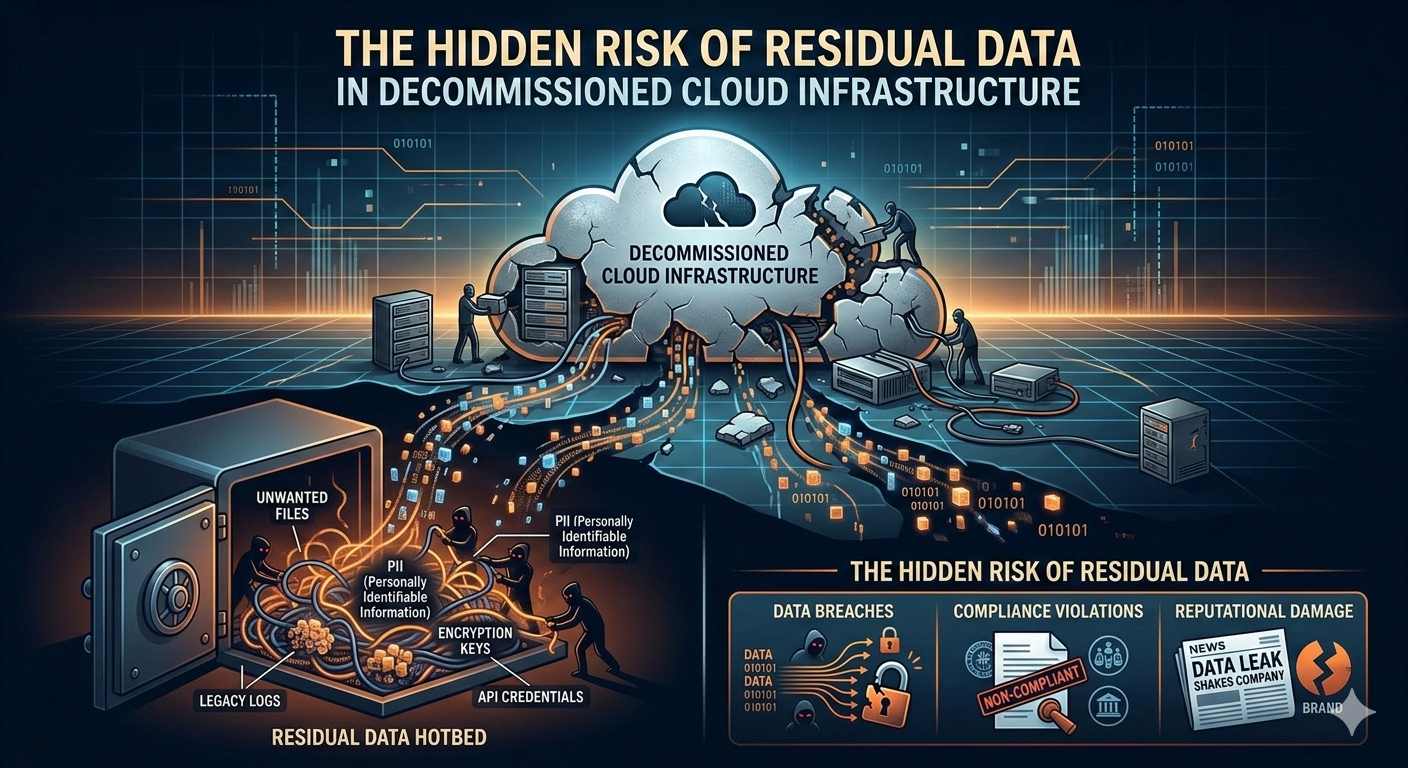
At this stage, many organizations focus on shutting down services and removing hardware. Yet one important issue is often overlooked: residual data.
Residual data is information that remains on storage devices even after systems are shut down or files appear to be deleted. Research shows that 68% of used storage devices still contain recoverable data, even when previous owners believed the information had been erased.
Understanding residual data and managing it correctly is an important part of modern cybersecurity and responsible technology management.
Understanding Residual Data in Cloud Infrastructure
Residual data is a simple concept, but it often surprises people. When you delete a file, the data itself may still remain on the storage device. The system simply marks that space as available for new data.
Until that space is overwritten, the original information may still exist in the background.
What Is Residual Data?
Residual data refers to leftover information that remains on a storage device after a system is shut down, replaced, or retired. It may remain on:
- Hard drives
- Solid-state drives (SSDs)
- Backup storage systems
- Virtual machine storage
- Cloud-based storage volumes
Even if a device appears empty, fragments of data can still exist.
Why Residual Data Happens
Residual data occurs for several reasons:
- Standard file deletion does not remove underlying data
- Virtualized environments create multiple copies of data
- Backup systems retain older versions of files
- Decommissioning processes sometimes focus on hardware removal rather than data sanitization
Because modern cloud environments are complex, it can be difficult to track where every copy of data is stored.
Why Decommissioned Infrastructure Still Holds Valuable Data
Organizations often assume that once a server or cloud instance is shut down, the data is gone. In reality, the storage devices used by those systems may still contain valuable information.
The Lifecycle of Cloud Infrastructure
Most IT infrastructure follows a predictable lifecycle:
- Deployment – systems are installed and configured
- Operation – systems run daily workloads
- Maintenance – upgrades and patches are applied
- Retirement – hardware or environments are replaced
During retirement, companies may remove equipment or migrate data to new platforms. However, the original storage devices often remain intact.
If those devices are reused, resold, recycled, or discarded without proper sanitization, the remaining data may still be recoverable.
The Security Risks of Residual Data
Residual data creates risks that many organizations underestimate. These risks extend beyond technical concerns and can affect business operations, compliance, and reputation.
Data Breaches
Improperly wiped devices have been the source of many security incidents. When storage devices leave a facility without proper data removal, attackers may recover the information stored on them.
In some cases, discarded hardware purchased on secondary markets has contained sensitive corporate data.
Regulatory Violations
Data protection regulations require organizations to manage personal information responsibly throughout its entire lifecycle. This includes the final stage when infrastructure is retired.
Examples of relevant regulations include:
- GDPR (General Data Protection Regulation)
- HIPAA (Health Insurance Portability and Accountability Act)
- PCI DSS (Payment Card Industry Data Security Standard)
If an organization fails to remove data properly before disposing of hardware, it may face regulatory penalties.
Reputational Damage
Data incidents do not only affect compliance. They also affect public trust.
Customers expect organizations to protect their information. If residual data leads to a breach, the resulting loss of trust can be difficult to rebuild.
The Role of Data Center Decommissioning
Data center decommissioning is the structured process of shutting down and removing IT infrastructure safely. This process includes more than turning off servers or removing racks of equipment.
It also involves managing data, hardware, and environmental considerations.
Key Steps in a Secure Decommissioning Process
A responsible decommissioning process typically includes several steps:
- Asset Inventory
Organizations first identify every device that stores data. This includes servers, storage arrays, backup systems, and networking equipment. - Data Migration
Important data is transferred to new systems or cloud platforms before the old infrastructure is retired. - Secure Data Erasure
Storage devices are wiped using certified methods that remove all recoverable information. - Physical Destruction When Necessary
In some cases, devices may be physically destroyed to ensure data cannot be recovered. - Responsible Recycling
Hardware components are recycled according to environmental guidelines. - Compliance Documentation
Organizations maintain records showing that data removal procedures were completed properly.
A structured approach helps reduce security risks and ensures that the process meets regulatory requirements.
Best Practices for Preventing Residual Data Risks
Organizations can reduce the risk of residual data by adopting clear policies and procedures. These practices help ensure that infrastructure retirement does not create new security problems.
Conduct a Full Data Audit
Before retiring any system, companies should review where data is stored. This includes:
- Primary storage systems
- Backup servers
- Virtual machine snapshots
- External storage devices
A complete audit ensures that no hidden data sources are overlooked.
Use Certified Data Erasure Methods
Simple deletion is not enough. Instead, organizations should use certified data erasure techniques such as:
- Multi-pass overwriting
- Cryptographic erasure
- Secure firmware-based wiping
These methods ensure that the original data cannot be recovered.
Maintain Clear Documentation
Documentation is important for both security and compliance.
Organizations should record:
- Devices that were sanitized
- Methods used for data erasure
- Verification results
- Certificates of destruction when applicable
This documentation demonstrates responsible data management.
Partner With Experienced Specialists
Decommissioning complex infrastructure can be challenging. Many organizations rely on experienced service providers to manage the process securely.
Specialists understand regulatory requirements and follow standardized procedures for data removal and equipment disposal.
The Importance of Responsible Data Disposal
Infrastructure retirement is not just a technical process. It is also part of responsible digital governance.
Organizations must prioritize secure data disposal when decommissioning data center infrastructure to ensure that sensitive information does not remain accessible after systems are retired.
Responsible data disposal protects several important areas:
- Customer privacy
- Corporate intellectual property
- Regulatory compliance
- Environmental sustainability
By treating data disposal as a core part of infrastructure management, organizations strengthen their overall security posture.
Companies that build responsible technology strategies often focus on the full lifecycle of digital systems—from design and operation to retirement.
Emerging Challenges in Cloud Infrastructure Retirement
As cloud environments grow more complex, new challenges continue to emerge.
Multi-Cloud Environments
Many organizations now use multiple cloud providers. Data may exist across several platforms at once. When infrastructure is retired, tracking all copies of that data becomes more difficult.
Virtual Machine Snapshots
Snapshots capture the state of a system at a specific moment. These snapshots may contain hidden copies of files, credentials, and system configurations.
If they are not deleted or sanitized properly, they can become an overlooked source of residual data.
Backup Storage Risks
Backup systems are designed to preserve data for long periods of time. However, old backups may remain active long after the systems they support are retired.
Without proper review, these backups can continue storing sensitive information indefinitely.
How Organizations Can Build a Safer Decommissioning Strategy
Managing residual data risks requires planning and coordination between different teams. A structured strategy can help organizations retire infrastructure safely.
Establish Clear Data Governance Policies
Companies should define clear rules for how data is stored, managed, and deleted throughout its lifecycle.
Policies should include procedures for system retirement and hardware disposal.
Train IT and Security Teams
Employees responsible for infrastructure management must understand secure data removal techniques.
Regular training ensures that teams follow best practices during decommissioning projects.
Integrate Security With Infrastructure Planning
Security teams should be involved in every stage of infrastructure lifecycle planning. This ensures that data protection remains a priority when systems are upgraded or replaced.
Conduct Periodic Audits
Routine audits help organizations confirm that their decommissioning procedures are effective. Audits also identify gaps where residual data risks may still exist.
The Future of Data Infrastructure Security
As organizations continue to rely on digital infrastructure, responsible data management will become even more important.
Several trends are shaping the future of infrastructure security:
- Stronger global data protection regulations
- Automated data sanitization technologies
- Increased focus on sustainability in hardware disposal
- Greater awareness of digital lifecycle management
These trends encourage organizations to treat infrastructure retirement as a strategic process rather than a simple technical task.
Conclusion
Residual data is a hidden risk that many organizations overlook when retiring cloud infrastructure and data center systems. Even after servers are shut down, storage devices may still contain sensitive information.
Without proper safeguards, this leftover data can lead to security breaches, regulatory violations, and loss of trust.
A responsible decommissioning process addresses these risks through careful planning, certified data erasure methods, and clear documentation. Organizations that prioritize secure data management throughout the entire infrastructure lifecycle can protect both their information and their reputation.
As digital systems continue to evolve, managing the final stage of infrastructure life will remain a critical part of modern cybersecurity.