Introduction
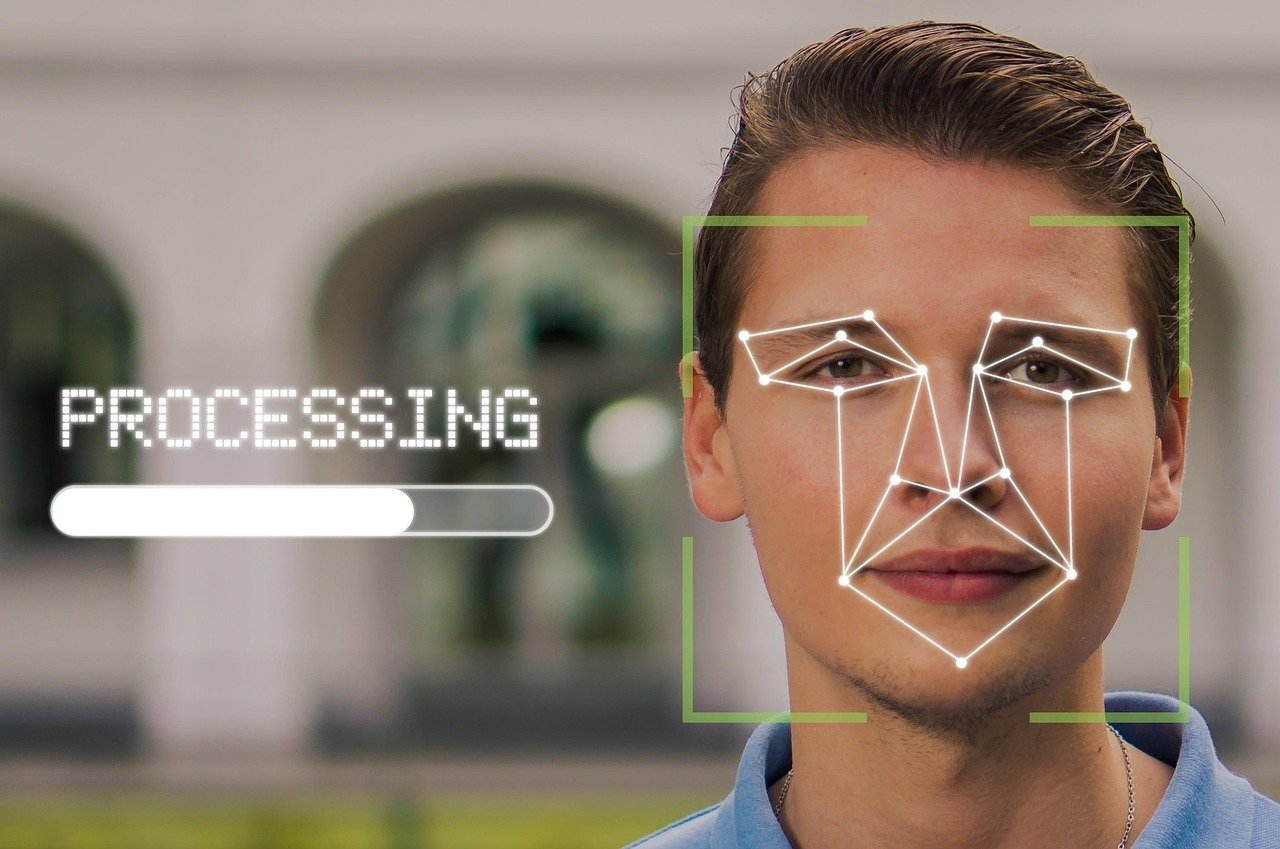
Face biometric software has quietly moved into daily life. People look at their phone to unlock it, walk through automated gates at airports, or confirm identity during remote registration. In each of these situations, software is analyzing facial features to answer a simple question: “Is this really the right person?”
Face biometrics means using the measurable patterns in a person’s face to recognise or verify them. Unlike older systems that depend on plastic cards or passwords, face recognition works with ordinary cameras and the face a person already has. That mix of convenience and security is a key factor behind its success.
To see how face recognition fits within a broader set of identification methods such as fingerprint, iris, voice and palmprint technologies, you can explore biometric solutions that bring these methods together.
How Face Biometric Software Works
Behind the scenes, a modern face system follows a simple chain of steps.
From camera image to face detection
Everything starts with an image from a camera. This could be a live video stream at a border gate or a single selfie taken during an app sign up. The software first analyzes the image to detect any faces and to extract them from the background. It inspects if the face is big enough, sufficiently sharp and properly lit.
Creating a face template
Once a face is detected, the software maps essential key points: eye corners, nose tip, mouth shape, jawline and related marks. It then turns these patterns into a National identity and citizen services.
Governments use face biometrics for national identity registers, voter lists and social programs. By tying each record to a unique face, authorities can:compact mathematical “template.” This template is not a normal picture. It is a coded representation that can be compared against other templates in a database.
Good systems can store several templates for the same person taken at different ages, with and without glasses or with changing facial hair. This helps the system stay accurate over time.
One to one vs one to many matching
Face templates are used in two main ways:
- One to one verification
The question is “Does this face match this claimed identity?” For example, a phone checks that the person holding it is the same one who registered earlier. - One to many identification
The question is “Who is this person among all known users?” The system searches a large gallery of templates, such as a voter list or a watch list, and returns the closest matches.
Both tasks are measured by independent test bodies. In well regarded evaluations, strong algorithms rank among the most accurate in both one to one and one to many scenarios, even in hard conditions like profile images or faces with masks.
Liveness checks and anti spoofing
A key concern is spoofing with printed photos or video replays. To address this, many solutions add liveness detection:
- Passive liveness checks subtle signals while the person simply looks at the camera, such as natural eye movement, small head motions and texture clues.
- Active liveness asks the person to blink, turn their head or follow on screen prompts.
Some systems also use checks inspired by passport photo rules, focusing on image quality and pose. If liveness fails, no face template is created and the attempt is rejected. For more details about liveness methods and test results, you can click here.
Why Face Biometrics Has Become So Popular
Several practical reasons explain the rise of face biometric software.
Contactless and hygienic
People have become more aware of hygiene and shared surfaces. Face checks do not require touching a reader, keypad or card scanner. This is attractive for busy sites such as office lobbies, hospitals, factories and border control points.
No passwords, cards or tokens
Passwords are forgotten, cards are lost and tokens are shared. A face is always with the user. This reduces help desk calls, badge reprints and support costs. It also removes common weak points in security, such as sticky notes with passwords under keyboards.
Mature accuracy and speed
Years of research and large scale testing have lowered error rates and increased speed. Elite engines can process large galleries in real time and still maintain low false match rates. That maturity allows governments and enterprises to trust face biometrics in serious, high volume projects.
Fits into existing cameras and systems
Most buildings and devices already have cameras. Face biometric engines can often use these without major hardware upgrades. The software can be integrated into access control panels, mobile apps, web portals and backend systems through standard interfaces.
Industry Applications and Benefits
National identity and citizen services
Facial biometrics are used by governments for national identity databases, voter registers and welfare programs. By linking every record to a unique face, authorities can:
- Prevent duplicate registrations
- Detect underage or fraudulent enrolments
- Protect the fair distribution of benefits
This supports cleaner elections, more reliable statistics and better planning of public services.
Border control and travel
In border control, face recognition helps match a traveler’s live face to the image in their travel document. Used in e‑gates and inspection booths, it allows:
- Faster passenger flow at airports and seaports
- Stronger checks against impostors using stolen passports
- Flexible handling of both supervised lines and self service kiosks
Independent test programs have measured performance in scenarios such as “visa vs border” or “border vs kiosk” with long time gaps between photos, showing that modern systems can handle real travel conditions.
Law enforcement and public safety
Law enforcement agencies apply face biometrics in controlled ways to support investigations. Typical uses include:
- Searching mugshot databases for a suspect image
- Linking repeated offenders across cases over many years
- Analysing video evidence more efficiently
When combined with clear legal rules, audit logging and human review, these tools can reduce investigation time while keeping accountability in place.
Banking and digital onboarding
Banks and fintech firms rely on face biometrics to secure remote services. Examples include:
- Online account opening by matching a selfie to an ID document
- Step up checks for high value transfers or changes of contact details
- Safer login to mobile banking apps without one time codes or static passwords
This cuts manual review costs, lowers fraud risk and gives customers a smoother experience.
Workplace attendance and access control
Face based attendance systems help employers track working hours reliably. They can:
- Stop “buddy punching” where one worker clocks in for another
- Combine time tracking with access to doors, turnstiles and parking
- Provide clear time sheets and attendance reports for payroll and audits
Because employees just walk up to a terminal and look at it, lines move faster than with card based or fingerprint systems. Multi biometric solutions even allow backup methods when needed.
Everyday device security and consumer apps
On the consumer side, face recognition secures phones, laptops, smart locks and even cars. People use their face to:
- Unlock a device
- Confirm payments
- Sign into apps and websites
Developers can make face checks into gaming, education, health and welfare apps to customise content or minimum access to definite features.
Practical Tips for Companies
What to look for in a face biometric engine
When selecting a solution, organisations should focus on:
- Independent evaluation results for both one to one and one to many tasks
- Robust liveness detection that is certified against recognised standards
- Performance in challenging conditions such as masks, profile views and poor lighting
Pilot projects are convenient for testing genuine user flows before a complete rollout.
Privacy, consent and user trust
Biometric data is sensitive. Responsible use requires:
- Clear explanation of what is collected and why
- Written policies for data storage, access and deletion
- Strong encryption and access control
- Options for alternative login methods where possible
By managing biometrics as part of a comprehensive trust strategy rather than just a security feature, companies can reduce backlash and secure long term acceptance.
Conclusion
Face biometric software has established it value across all industries by providing strong security, user-friendly actions and helpful scalability. From national identity systems and border security to employee attendance and financial services, it helps organisations know who they are dealing with and deliver services with less friction.
Success is not driven by technology alone. It depends on well-planned designs, a careful process of selecting vendors and a strong foucs to data privacy and ethical responsibility. When those elements are in place, face biometrics can safeguard organisations and users while helping make daily interactions faster and easier.